Voting Machines Helpfully Had Same Thingamajig That Let You Remotely Control Your Old Dad's Puter
Some things actually DID work better before computers.
One of the largest manufacturers of voting machines has admitted it sold election-management systems with software that allowed remote access via the internet. They're pretty sure nobody hacked into a state election, but they're also not sure.
From 2000 to 2006, Election Systems and Software (ES&S) sold a specialized computer with a program that allowed tech support geeks to dial into election systems and take control. ES&S says that the program, pcAnywhere, was only installed on a "small number" of the voting systems sold during that time, and they only put the program there so some nerd could fix glitches or send updates. The only problem is that we're just now finding out, and ES&S is being very shady after being caught with their pants down.
ES&S says that they stopped using pcAnywhere in 2007 after the Election Assistance Commission changed voting standards in 2005. Yet public records show they signed a contract with at least one state in 2006 that specifically said they could use the program for "software support calls that cannot be resolved over the telephone." It wasn't exactly criminal to sell software they knew had dangerous holes large enough to drive a truck through, but it is a bit mysterious.
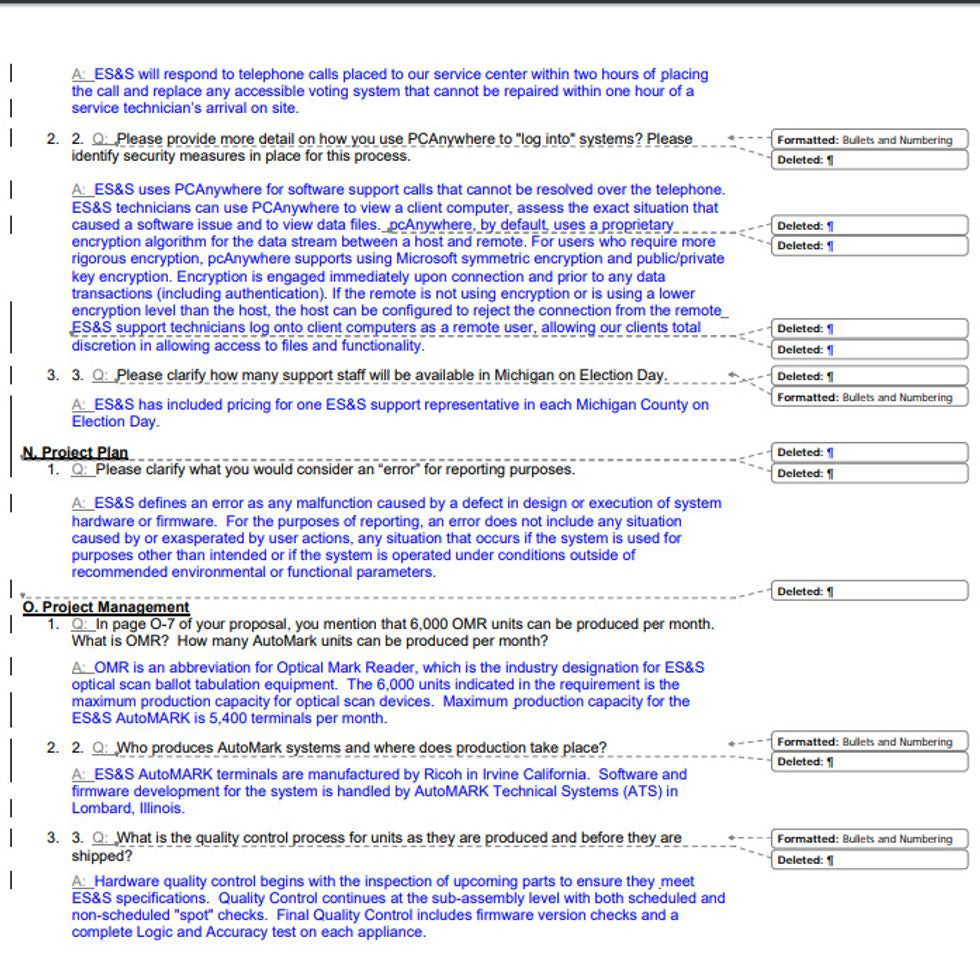
A contract between ES&S and the State of Michigan from January 2006
At the same time ES&S was still installing pcAnywhere on a "small number" of computers in 2006, some hackers actually stole the source code. Like DNA, the source code is the program, holding instructions on what to do, how, and when. ES&S didn't bother to mention the code had been stolen until 2012, and only after part of the code showed up online. Symantec, which actually created the pcAnywhere software, immediately told users to turn off or delete the program; ES&S didn't do squat. Shortly after the code appeared online, some nerds found a bug in it that allowed enterprising SOBs to take control of any system with pcAnywhere. Ooops.
The election management systems used by ES&Sare notthe voting machines most of us use in a polling booth. They're the computers that crunch numbers and tabulate votes so that grandmas don't have to sit in an elementary school lunchroom until 3: 00 a.m. on election night.
For security reasons, election management-systems and voting machines are not connected to the internet. This is called an "air gap," and it is supposed to prevent someone from breaking into a computer and poking around. As long as computers remain unconnected to the internet, the only way they can talk to the outside world is through something like a thumb drive, or by connecting a bunch wires. It's not 100% safe, but it's closer.
Silly internet, you can't see this computer!
ES&S is now in damage control and refusing to talk publicly about whether or not any of its customers were using pcAnywhere during the 2016 election, but records show the software was installed on some systems as recently as 2011. Instead, they've offered to chat privately with Sen. Ron Wyden, the loudest voice on e-voting fuckery. After hearing that ES&S had sold election systems with remote access software baked in, Wyden told reporters it was "The worst decision for security short of leaving ballot boxes on a Moscow street corner."
While ES&S purposely installed this hole in their software, cyber security experts have been warning that simply downloading updates and software patches puts other election systems at risk. Even uploading unofficial voter talleys on election night creates a big risk as the data and the system can be seen by other computers. Though those kinds of attacks don't really affect the voting machines the rest of us use, they're vulnerable to other attacks that don't require much time, money, or nerd super powers.
Voting machine companies are trying to calm growing fears of electoral shenanigans by stressing how complicated it is to mess with an election. But cybersecurity experts point to old and outdated voting systems, shady practices by local officials, a lack of security protocols , and an ignorance of basic cybersecurity as proof that it's actually really easy to screw with an election. The Election Assistance Commission hasn't said much about election hacking, but Robert Mueller did when he indicted 12 Russian military intelligence officers for spear phishing attacks aimed at election officials, and for screwing with 39 state votings systems.
A very dubious history surrounds e-voting systems, and calls for paper trails are growing among cybersecurity experts . As we learn just how vulnerable the democratic process has become, there are tools that allow you to check what voting machines your district uses . Good-guy hackers have been tinkering with voting machines for years, and the largest hacker convention in the world, DefCon, is inviting state election officials to learn how to hack voting machines in the interest of education and safety next month. Public officials may not be taking this stuff seriously, but there are some angry nerds who do.
[ Motherboard ]
Wonkette is ad-free and reader-supported, and we're all about taking apart our toys to see how they tick.



That's how it was done in my county for decades. But then they switched to electronic touch-screen voting machines. I think it is easy to make a mistake on those machines.
And of course nobody in the Voter Registration office is computer literate, so it is all handled by an outside IT firm they have a contract with. I doubt anyone in the County understands the ins-and-outs of computer security, they have to trust what the contractor tells them.
The districts I've voted in went back to paper ballots years ago. Sure it costs money, but that means someone's making money. (Probably someone who's friends with the lawmakers, but whatever.) The ballots are scanned as you turn them in, and then stored. They are only handled if analysis of the scanned date raises a red flag. I'm in IT and I think this is a good way to go. Redundancy.