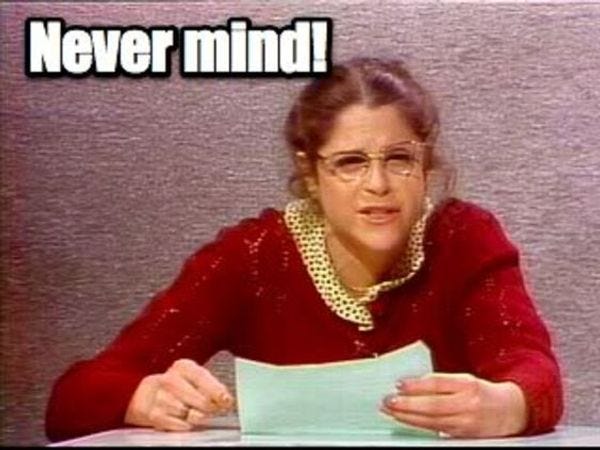
Vermont Utility Wasn't Hacked By Russia After All. Also, Stop Worrying About Endangered Feces.
And why should you see a doctor if an election lasts four hours? That seems very efficient!
Welp, turns out you really can't believe anything you read in the lamestream media ever, since the Washington Post has retracted a story about possible Russian attempts to hack into a computer at a Vermont power utility. Here's how the erroneous report came about:
An employee at Burlington Electric Department was checking his Yahoo email account Friday and triggered an alert indicating that his computer had connected to a suspicious IP address associated by authorities with the Russian hacking operation that infiltrated the Democratic Party. Officials told the company that traffic with this particular address is found elsewhere in the country and is not unique to Burlington Electric, suggesting the company wasn’t being targeted by the Russians. Indeed, officials say it is possible that the traffic is benign, since this particular IP address is not always connected to malicious activity.
Officials investigating the laptop say they found it contained malware often associated with criminal activity, but that it was not, as had originally been reported, connected with "Grizzly Steppe," the Russian hacking operation. (But you still have to admit that's a cool codename.) Burlington Electric officials said Friday the code found on the laptop appeared to match a warning sent to power companies and other industries by the Department of Homeland Security, but then over the weekend said only that they'd "detected suspicious Internet traffic" on the computer. To make matters worse, the Washington Post's initial report on the incident said the power grid itself had been hacked, although it quickly corrected that portion of its story Friday when the utility said the laptop had not been connected to the grid.
Is there more? Yup! Says WaPo:
The murkiness of the information underlines the difficulties faced by officials as they try to root out Grizzly Steppe and share with the public their findings on how the operation works. Experts say the situation was made worse by a recent government report, which they described as a genuine effort to share information with the industry but criticized as rushed and prone to causing confusion. Authorities also were leaking information about the utility without having all the facts and before law enforcement officials were able to investigate further.
The government report did at least include a caution that the suspicious IP addresses it listed weren't definitive proof of bad internet things happening: “Upon reviewing the traffic from these IPs, some traffic may correspond to malicious activity, and some may correspond to legitimate activity.” Critics of the report have said it may have been so overly broad as to not really help companies trying to improve their security. Yep, sounds like! As a matter of fact (a phrase we're no longer comfortable with at all), roughly 30 percent of the IP addresses listed in the report
were commonly used sites such as public proxy servers used to mask a user’s location, and servers run by Amazon.com and Yahoo. [...] The IP address information alone is not useful, experts noted. Moreover, a server that is used by Russian spies one year might be used by “granny’s bake shop” the next, Lee said.
So it looks like the utility found one of those IP addresses and reported it, mistakenly thinking the Russians Were Coming all over one of its computers. Then the leaks started, from people who may not have really known all the details. Oops. And for the sake of irony, a DHS official who of course spoke anonymously to the Post said the erroneous story from Vermont shouldn't dissuade other companies from sharing information out of fear it will be leaked; the official said the Vermont utility "did what it was supposed to do."
That anonymous official also defended the government report warning companies to look out for suspicious network traffic, since
“We know the Russians are a highly capable adversary who conduct technical operations in a manner intended to blend into legitimate traffic,” the official said. The indicators of compromise contained in the report, he said, “are indicative of that. That’s why it’s so important for net defenders to leverage the recommended mitigations contained in the [report], implement best practices, and analyze their logs for traffic emanating from those IPs, because the Russians are going to try and hide evidence of their intrusion and presence in the network.”
So, now that the Washington Post has corrected its story and explained where things went wrong, we can all look forward to a follow-on wave of wrong conclusions, like people insisting you can't believe a damn thing you read in the papers, ever. How do we even know the retraction is correct? Or that the CIA wasn't every bit as wrong when it attributed hacks of the DNC and Clinton campaign to the Russians? (Hints: The CIA is not a newspaper? And WaPo did issue a correction as soon as it determined it was wrong?) In this age of computer, nobody knows anything.
Also, since we have never been to this so-called "Vermont," we've got serious doubts it even exists.
[ WaPo ]



Haven't heard o' that 'un. Thanks!
They're not the cheapest, at $12 CAD for a relatively tiny pint jar, but they're as organic as can be and all-natural, and yes delicious.